Oh hey, look… a post. 🙂
Anyway, a couple of weeks ago, two at the time of this writing, I updated my Debian Gnu\Linux server running this site. It broke things. Instead of showing the site, the Apache server showed the text in index.php.
I was running WordPress 6.2 with PHP 8.2. Those two key points are essential because most of the documentation out there for the problem talks about Old versions of WordPress and Old versions of PHP. Neither of which fit me.
Going through sites, I found the fixes. The first was ensuring that PHP was set up in the Apache modules. The easiest way to set it up was to install Libapache2-mod-php8.2.
|
1 |
sudo apt install libapache2-mod-php8.2 |
This command changed the error from the index.php to an error:
Your PHP installation appears to be missing the MySQL extension, which is required by WordPress. Please check that the mysqli PHP extension is installed and enabled.
Again, searching said to update WP and PHP (both were already at the newest), so little help. Luckily I found something pointing to the WP support forum; someone with WP 6.2 and PHP 8.2 having the same issue. The volunteer support person, Steven Stern (sterndata) (@sterndata), said to check php-mysqlnd. The command he used, for that thread’s OP Centos box.
So one search and installation later, I’m back in business and updated to WP 6.2.2.
|
1 2 |
apt-cache search php-mysqlnd sudo apt install php8.2-mysql |
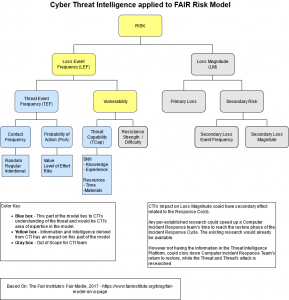
Now if I could just find my notes and remember everything, I was writing about CTI in January of 2022.
For those interested in root cause analysis: My last upgrade was for Testing to the newest level. It looks like some things with MySQL and php didn’t get updated right and broke the site. I just didn’t think to check if my site was working after the update.