I used to have a home lab of 3 cisco routers, and 3 cisco switches. That was for my CCNA training. Problem was, they were so old, they were not worth it. The lab also had 2 Intel 32-bit PC towers and a Sun Ultra 10. The Sun box was to get the Sun certification, but never got around to it. That isn’t to say that the lab wasn’t used. Just not used for the reasons I originally bought the components for.
Now, since I graduated and I have money to spend on building a new lab, I’m looking at getting something new set up. After watching Johnny X(m4s) and Eve Adams recorded talk from Derbycon. I decided on the following design.
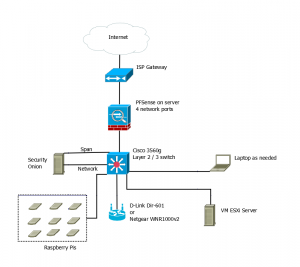
So this will be on a separate internet connection from my home network. That means getting a second line to the house, but it doesn’t have to be the fastest line in the world.
The hope is to have the PFSense box, the Security Onion Box, and the Vmware ESXi box all running on Micorservers. The price for the Lenovo ones are decent.
I want a Cisco 3560g switch for Gig out all the ports, plus the layer 2 / 3 routing. Again the price isn’t too bad, about the same as the Microsevers. Lastly if I decide to go for the CCNA again, it should be useful.
The wireless access point was chosen from the Offensive Security WiFu class hardware list. I could use my old Linksys WRT54GL with dd-rwt on it. But it cant’ do N. Granted it looks like the Off-Sec recommended ones are only half N.
Lastly, it would be nice to have a peg board with all my Raspberry Pi devices attached to it. Requires being easy to remove them, but not a big issue. This would give me a place to have them while working and store them when not in use. If I can get POE on the 3560g, that means I can get a POE splitter and adapter for each Raspberry Pi, and don’t have to worry about power there either.
The laptop would be as needed device. I could use my current one or buy one to dedicate to the lab. Mainly it’s there for user interface purposes than anything else.
The only downside, even though I’m not paying for college classes out of pocket any more, is that it will take a while to build this lab. I’m going to have to piece it together a little at a time.